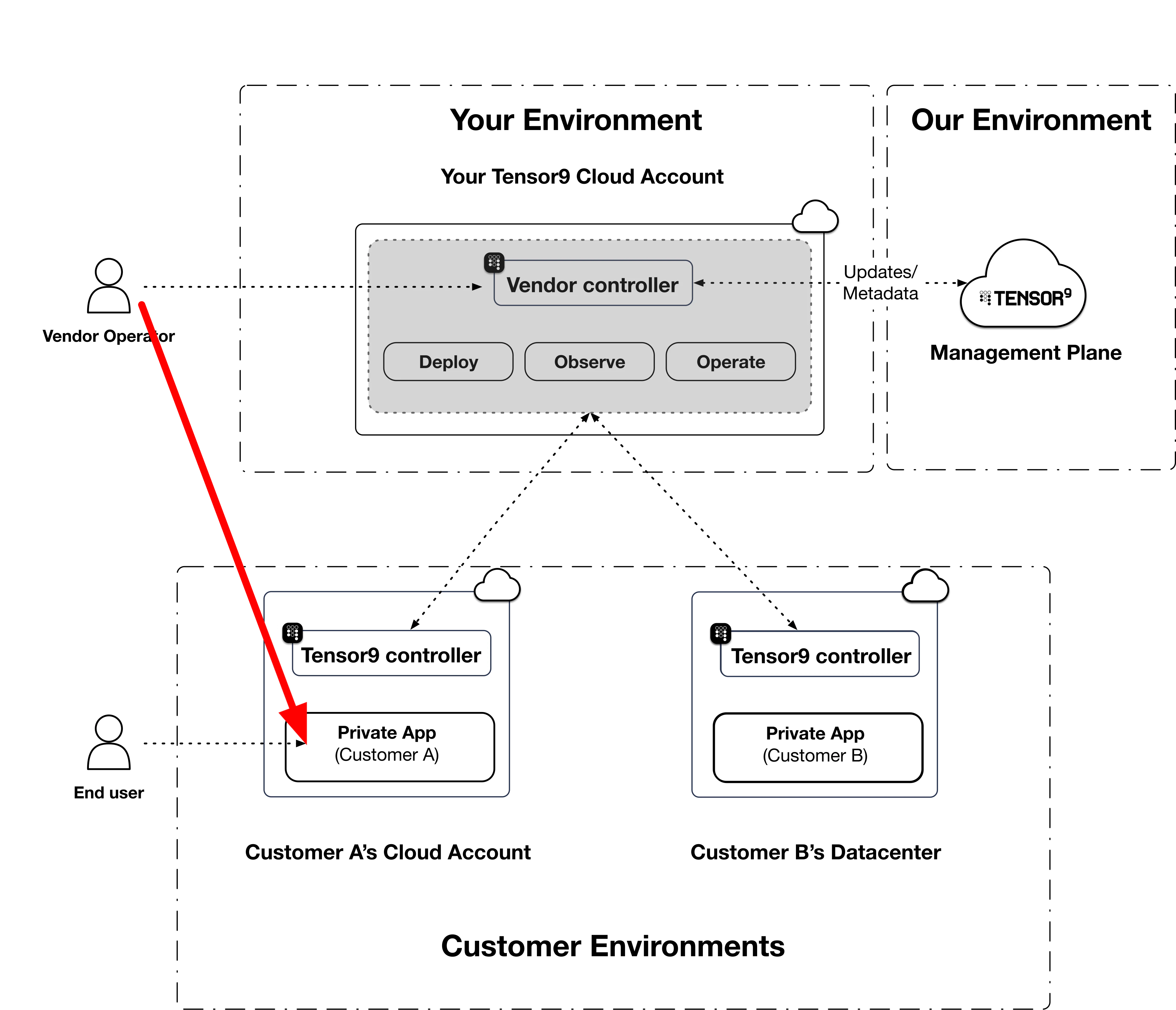
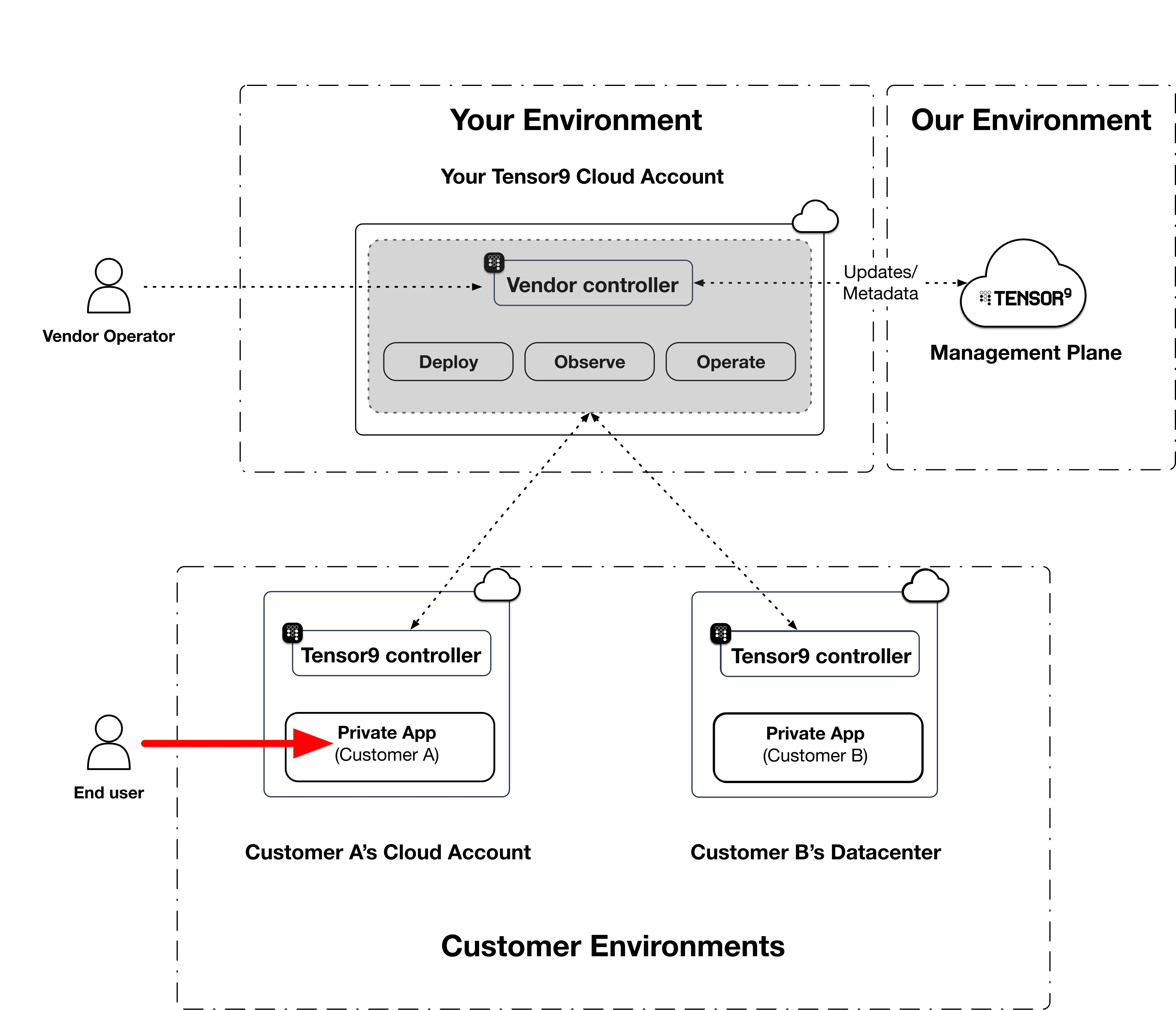
A Tensor9 deployment has four distinct network links with configurable paths. Each one carries a different kind of traffic, has different defaults, and exposes different options. This page covers them in one place so you can reason about them together.Documentation Index
Fetch the complete documentation index at: https://docs.tensor9.com/llms.txt
Use this file to discover all available pages before exploring further.
| Link | Direction | Used for |
|---|---|---|
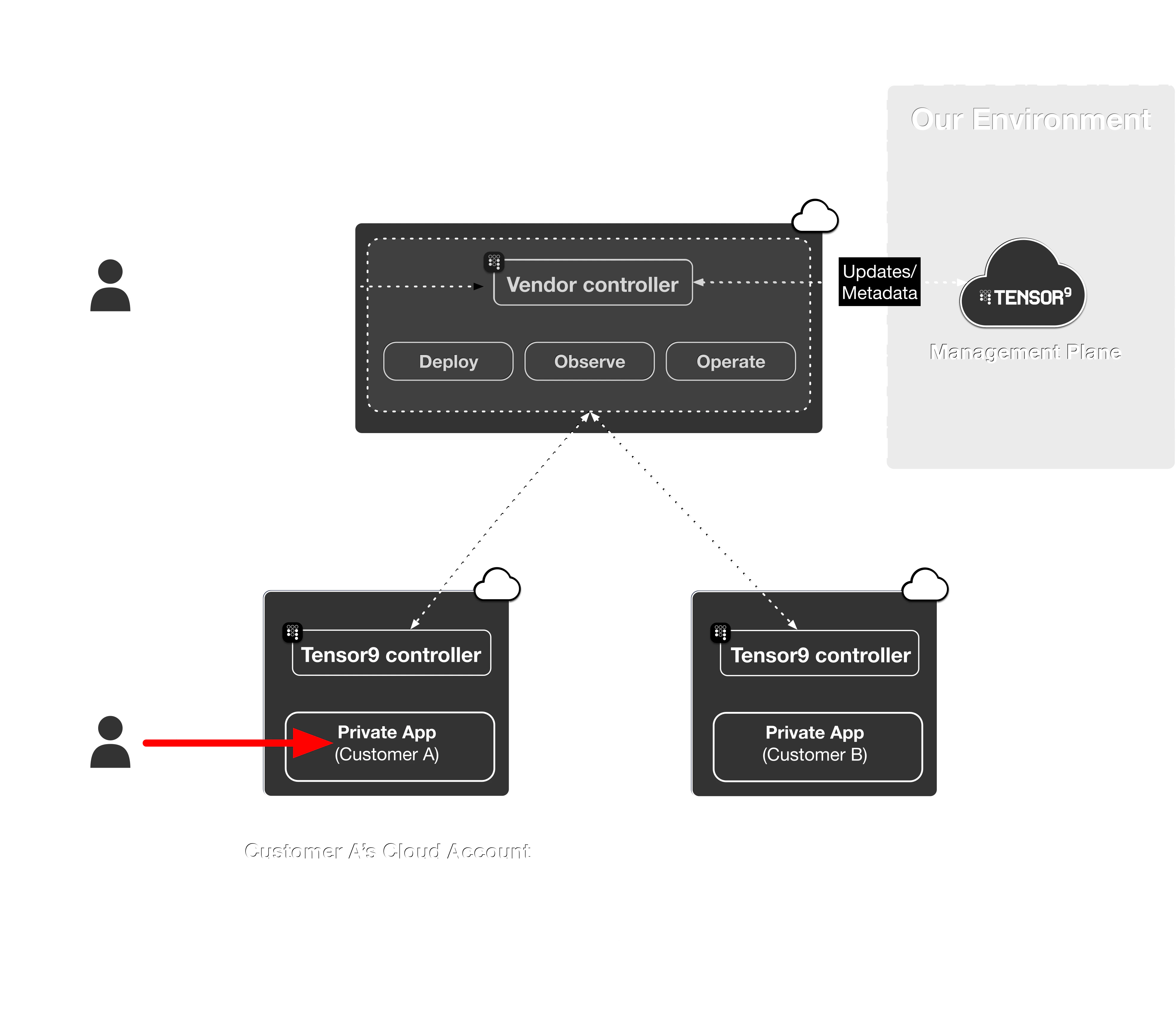
| Application ingress | Customer’s users to the deployed app | End-user traffic |
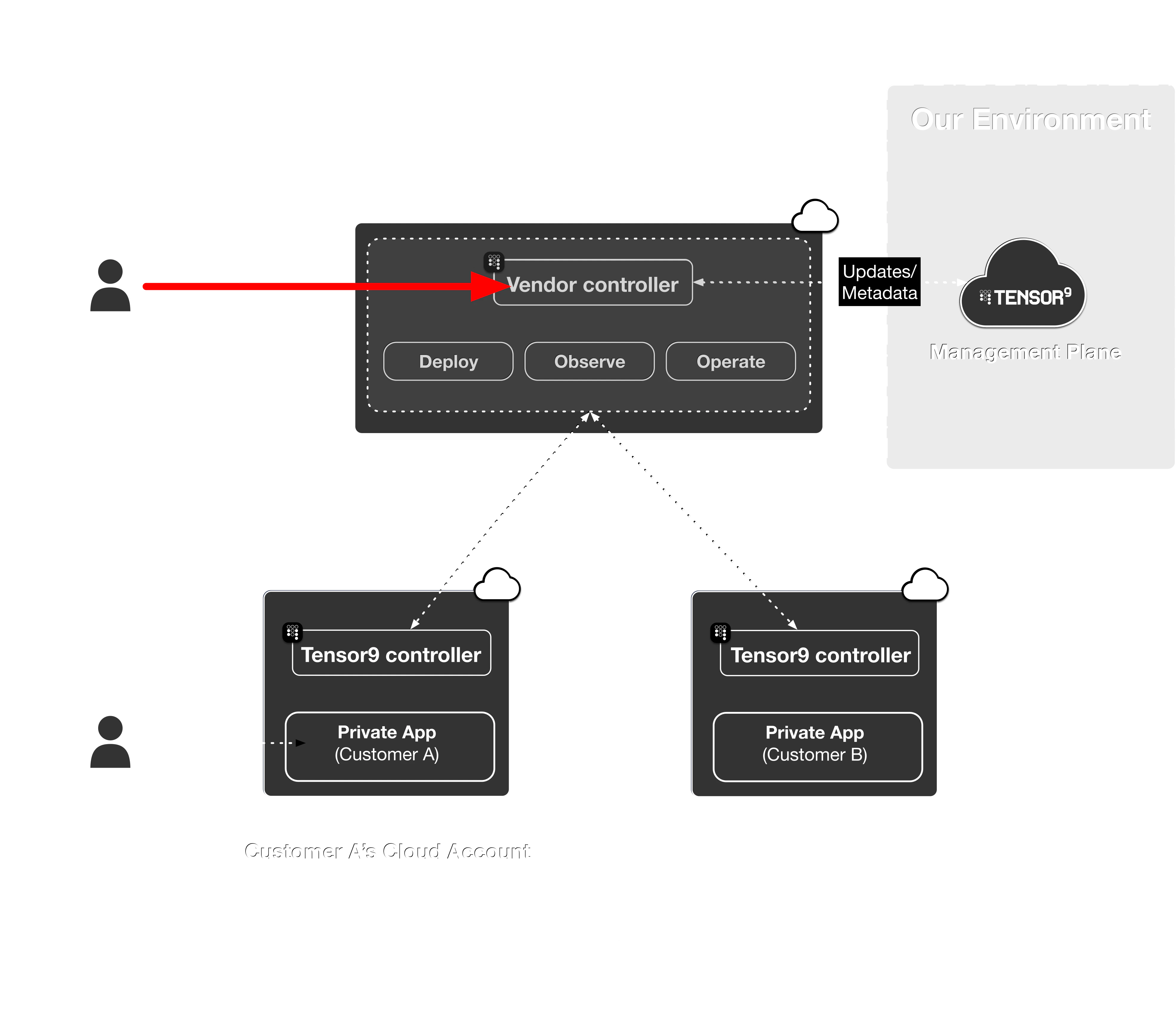
| Operator to control plane | Your CLI/IaC tooling to your vendor control plane | Day-to-day operations and deploys |
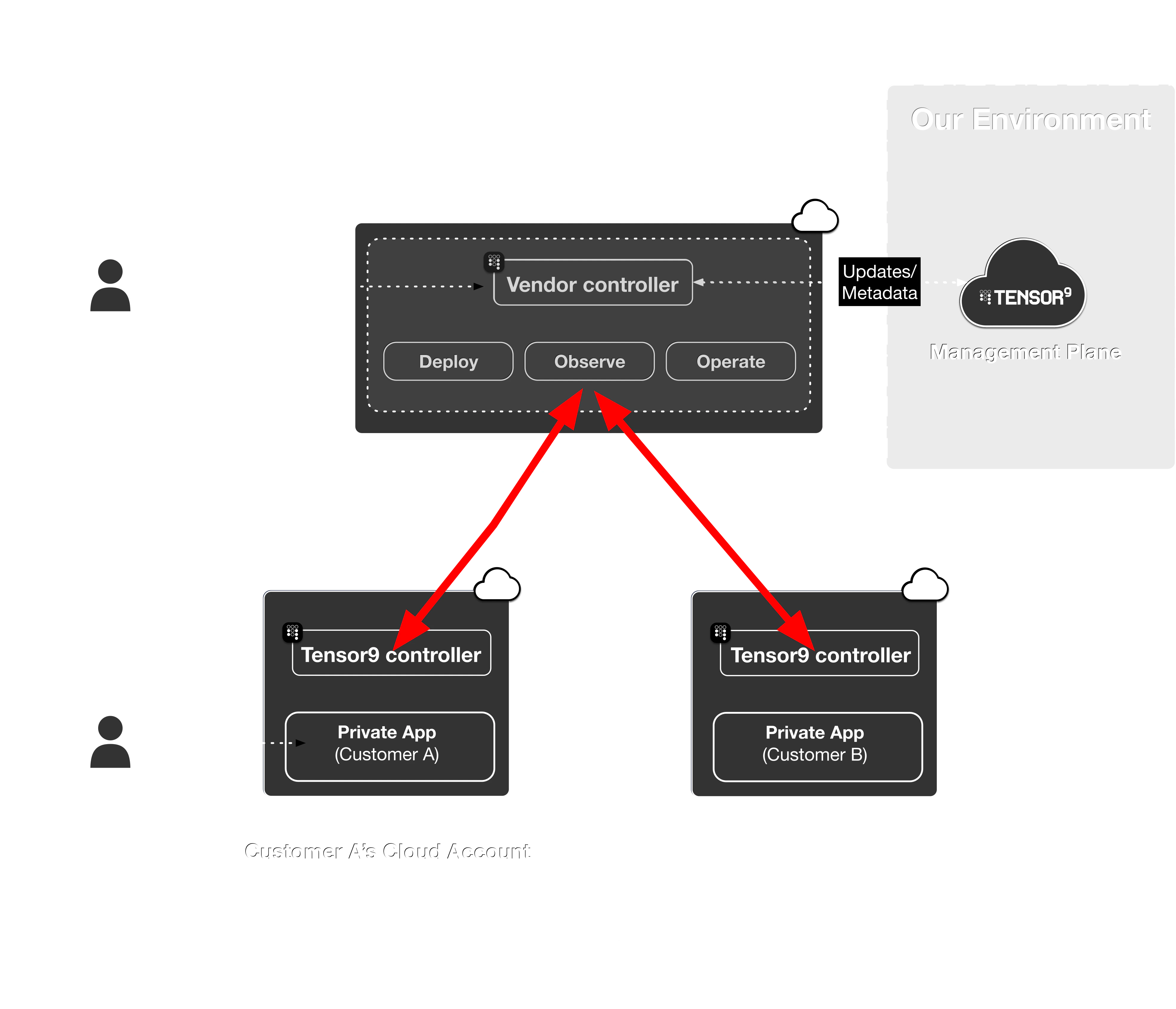
| Appliance to control plane | Customer’s appliance to your vendor control plane | Telemetry, deploy instructions, secure remote management |
| Break-glass access | Emergency operator access into the customer environment | Time-limited elevated support access |
Application ingress
Operator to control plane
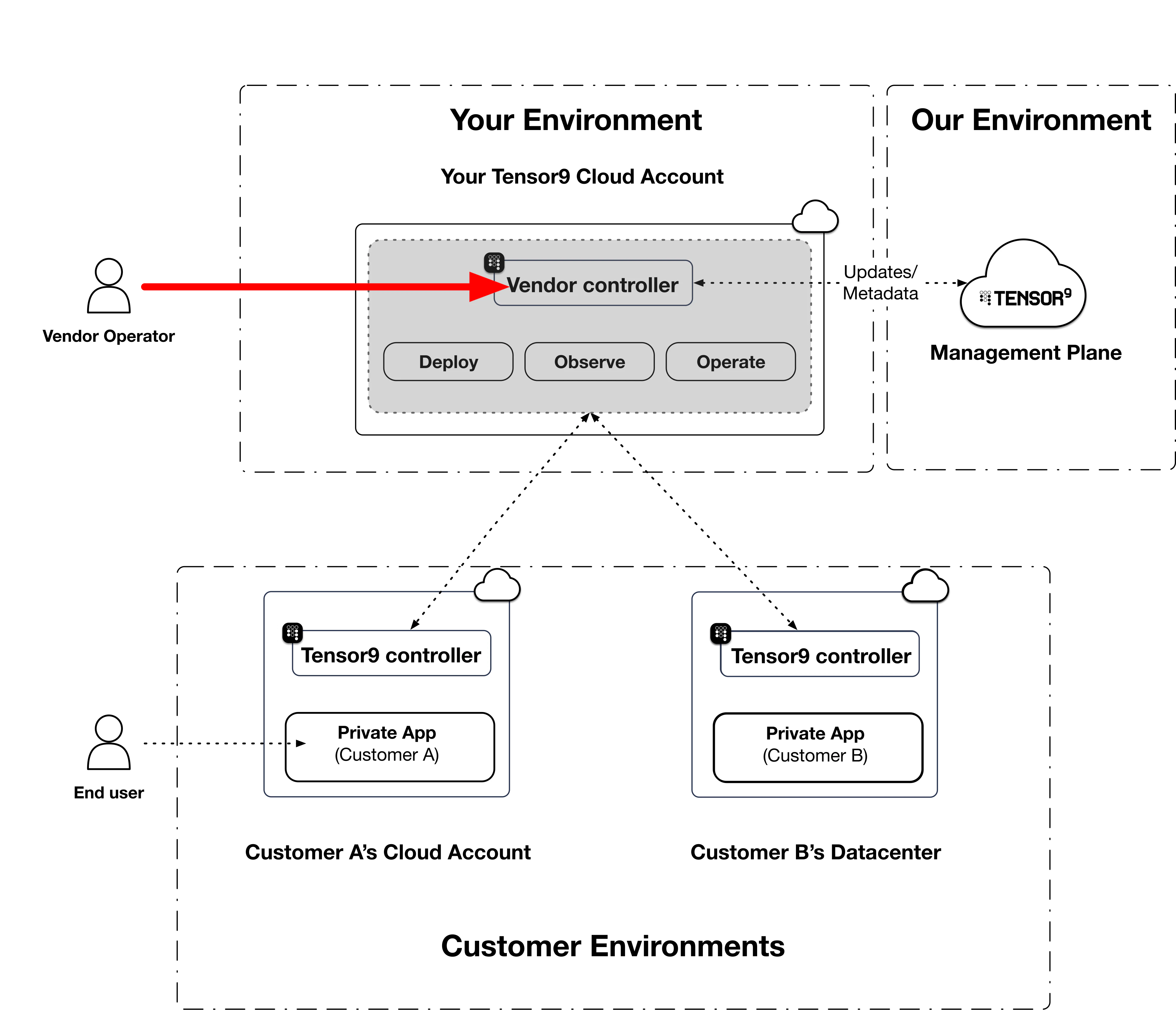
tensor9 commands, or when an origin-stack deploy executes its plan and apply against an appliance, your CLI talks to your vendor control plane. The control plane’s network surface exposes a small set of mutually-authenticated listeners for this traffic.
Default: public load balancer with mTLS
By default, the control plane’s listeners are reachable over the public internet via a network load balancer. Every connection is mutually-TLS authenticated using operator certificates that Tensor9 issues during enrollment. No public access is granted; the listener accepts only certificate-presenting clients on the operator allowlist.Optional: route operator traffic over Tailscale
If you operate a Tailscale tailnet for your engineering team, you can have your vendor control plane join that tailnet and expose the same operator listeners over it. Once joined, your operators can reach the control plane at its tailnet hostname without leaving Tailscale. A step-by-step guide to onboarding is provided in Common Workflows.Optional: remove the public path
After your operator tooling is reliably reaching the control plane over Tailscale, you can remove the public-internet path for the operator-side listeners:CLI, Terraform, and Appliance services. Each service is gated individually so you can roll out the change in stages. See our step-by-step guide to onboarding in Common Workflows for more details on this process.
Enforcing tunnel-only for the appliance-facing listener (the
Appliances group, which carries the appliance-to-control-plane link below) requires extra care. The command refuses to enforce that listener if customer appliances or appliance-setup links are still using a non-tunnel path, or if AWS PrivateLink is active for the appliance link. See the Appliance to control plane section for the relationship between the two.Appliance to control plane
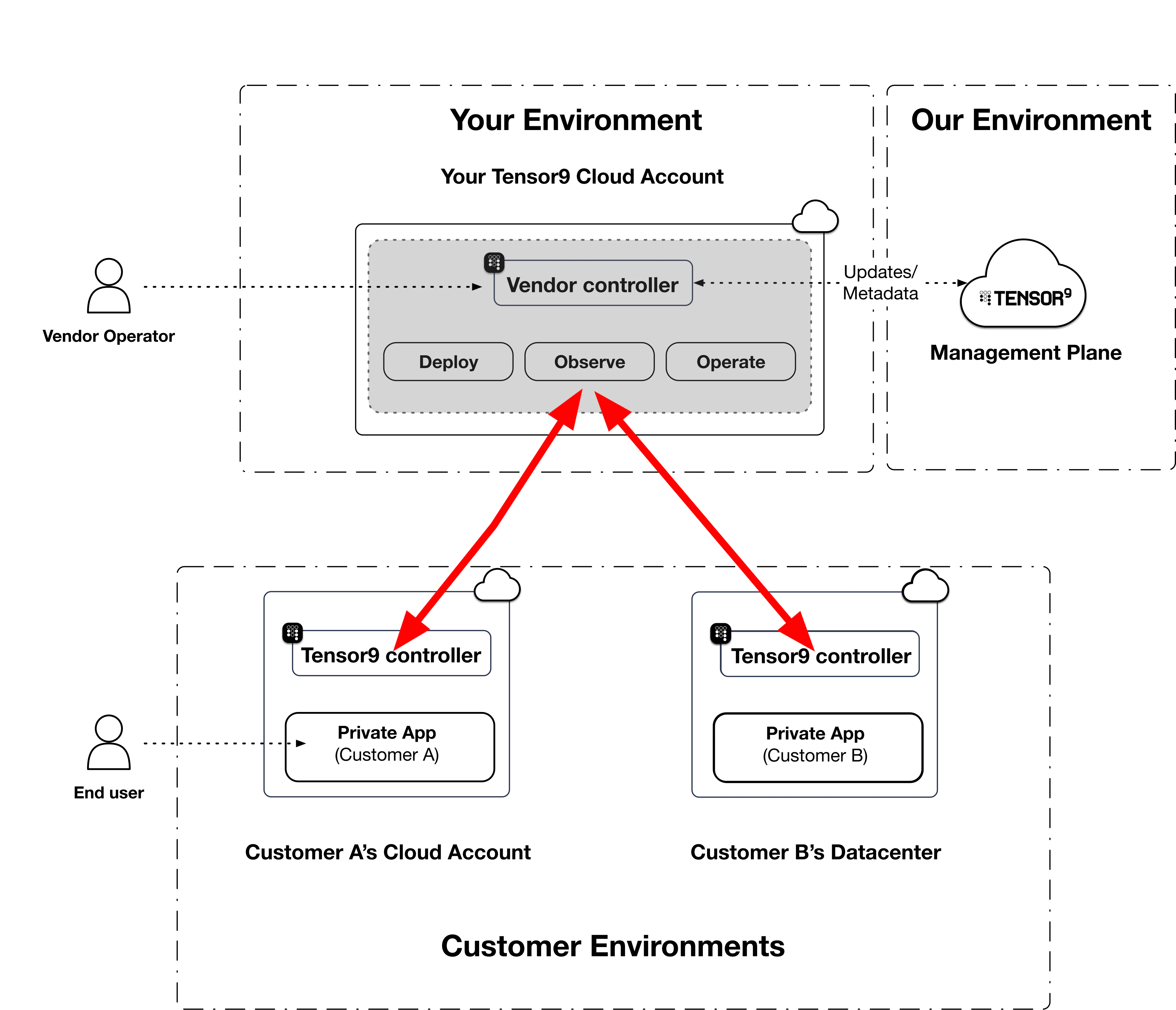
| Network path | Where it works | What it requires |
|---|---|---|
| Public internet | Any combination of vendor and customer environments | Outbound HTTPS from the customer environment |
| AWS PrivateLink | Vendor control plane and customer environment are both on AWS | Vendor opts in at setup; cross-region attachments supported |
| Tailscale (vendor-provided) | Any environment where the customer’s appliance can run Tailscale | Vendor-supplied tailnet that both the control plane and the customer’s appliance join |
Vendor-provided Tailscale (TailscaleVendor)
The vendor operates a tailnet. Both the vendor’s control plane and each enrolled customer appliance join it. The appliance-to-control-plane handshake then travels the tailnet instead of the public internet or PrivateLink.
This is particularly useful for:
- Test appliances and other vendor-operated environments where you want all appliance-to-control-plane traffic on a single private network you control.
- Customer environments that allow outbound Tailscale but prefer not to expose direct internet egress to the vendor control plane’s public listener.
TailscaleVendor-permitted form factor, you provide the buyer’s pre-auth key, and the customer’s appliance uses it at boot to join your tailnet.
Customer-provided tailnets
A symmetric variant where the appliance joins the customer’s tailnet viatsnet and the vendor control plane reaches into it is not yet available. Contact us if this would unblock a deployment; we’d be interested to talk through specifics.
Break-glass emergency access